In the present digital age, passwords are used the most as the methods of secure online identities. But also at the same time we are seeing an increase in data breaches and password fatigue at which point it is very much true to say that our present traditional password systems are no longer enough. Into this stage steps Decentralized Identity (DID) , a transformist approach that may at last do away with passwords and give users full control of their digital identities.
What is Decentralized Identity (DID)?
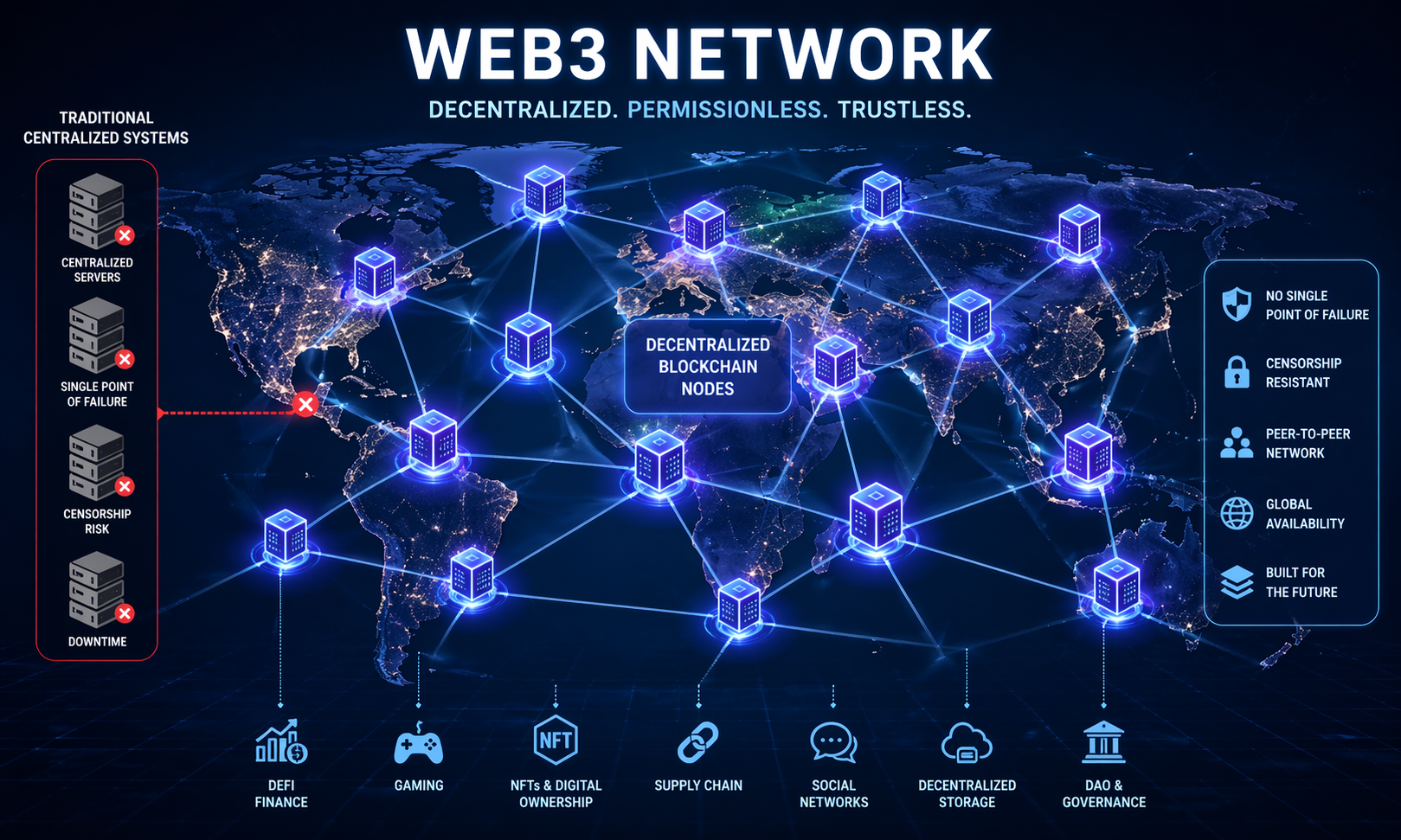
Decentralized Identity (DID) is an emerging model of digital identity which we see put forward by the use of blockchain and distributed ledger tech. In contrast to what we have in present systems which see your info stored in a central server that is run by a company, with DIDs you as the individual are in the driver’s seat. You may present your identity credentials, you may present or withdraw your information as you see fit without depending on a central authority.
In DID authentication takes place of a password which is stored in a company server. Instead we have cryptographic keys which prove your identity. This in turn means your private info stays private and we see a reduced chance of large scale data breaches. DID is also designed for use across many different platforms which means a single digital identity can be used across many services which in turn removes the need to remember many different passwords.
How DID Works
At the base of DID are three primary elements:.
- Cryptographic file which includes the public key of a user and other data which they put out. This document attests to the owner of an identity.
- Decentralised Identifier a unique string which identifies the user across systems while at the same time protecting personal information.
- Issued Digital Certificates which come from trusted entities like a university which has issued your degree or your state which has issued your driver’s license or a professional body which has issued your certification. These can be presented choice by choice without that of your other personal information.
When at login a user presents a verified credential which the service then uses for validation via cryptographic proofs as opposed to passwords. This approach does away with phishing issues and also greatly improves security.
Benefits of Decentralized Identity
Enhanced Security
DID does away with the use of stored passwords on servers which in turn reduces the issue of hack and leak. Also users do not have to use weak or which they have re-used passwords. With cryptography only the DID’s owner has the ability to access and put out their credentials.
User Control and Privacy
With DID people have full control over what info is shared and which parties it is shared with. Personal data does not have to be stored on many platforms which in turn reduces privacy risks. Also users may at any time revoke access to their credentials.
Simplified Digital Experience
DID presents a smooth login experience. Users are able to authenticate across sites, apps, and services which in turn removes the need to remember many passwords. Also this improves accessibility and for those that are not as tech oriented.
Interoperability Across Platforms
Decentralized identities we see as universal. A single DID can be used in finance, health care, education and more which in turn forms a whole digital identity ecosystem.
Future-Ready Identity Management
As we see more sectors adopt blockchain based identity solutions, DID is becoming the norm for secure, private identity management. Of governments and businesses alike we see the push for decentralized identity which in turn has us heading to a future in that digital interactions are at once trustworthy and seamless.
Potential Challenges
While DIDs show great promise, we see that adoption is not without its issues. Wide scale implementation requires that we see more industry cooperation, development of standards for interoperability, and a great job done in terms of user education. Also it is the issue of management of cryptographic keys which some users find to be a great challenge. We are seeing innovations like social recovery and secure key storage which are to help overcome these issues.
The Future of Identity Without Passwords

Decentralized Identity is out from the gate of technical improvement; it is a shift in the way we think of digital security and privacy. Through giving users what they need to run their own credentials, which in turn reduces our tie into large central databases, and we see also greater interconnectivity between what in the past have been isolated systems in that which we put forth Decentralized ID we see a safer, easier and more user friendly digital world. As more companies, governments and institutions buy into DID standards we are at a point of seeing the end of the password era.
Conclusion
The growth of Decentralized Identity is at a turning point in digital security. For a while passwords which we thought were very basic elements of security are now an issue in the hyper connected world. DID puts forth a secure, private, and user controlled option which in turn allows individuals to fully own their digital identities. As we see issues in adoption and user education still present, what we have is improved security, privacy, and easy access. In the not too distant future decentralized identity may become the norm which will create a digital environment in which users are true masters of their data and which sees the end of passwords.
FAQ
Will that be the password?
Yes we are seeing the aim of DID which is to put an end to the use of passwords in favor of crypto verification. Also adoption is slow but the technology is put in to do away with passwords completely.
Is DID secure against hackers?
DID is very secure in that it uses cryptography. Also unlike with passwords’ which are stored on central servers, did’s are not which in turn reduces the risk of large scale breaches or phishing.
How do I get back into my DID if I am locked out?
Many DID services provide for recovery which includes social recovery, trusted contacts, or hardware wallets which in turn means that users will not have access lost permanently.
May I use DID on various platforms?
Yes, in the case of decentralized identity interoperability is a key feature. A single DID can authenticate users across the web, applications, and services world wide.
Which entity has control of my personal data in DID?
Users are the only ones that have full control. We only access what you choose to share which in turn maximizes your privacy and personal data ownership.